Sensational AG is the company I founded together with a colleague back in 2000. Ever since then, we had a very nice combination of fun, interesting work and a very successful business.
We’re a very small team – just nine programmers, one business guy, a product designer, a frontend designer and two bloody excellent project managers. Me personally, I would love to keep the team as small and tightly-knit as possible as that brings huge advantages: Little internal politics, a lot of freedoms for everybody and mind-blowing productivity.
I’m still amazed to see what we manage to do with our small team time and time again and yet still manage to keep the job fun. It’s not just the stuff we do outside of immediate work, like Cola Double Blind Tests, Drone Flights directly from the roof of our office and much more – it’s also the work itself that we try to make as fun as possible for everybody.
We are looking for a new member to help us with the development of our main product, an eCommernce platform that’s optimized for wholesale customers.
We’re not about presenting a small amount of product in the most enticing manner, but we’re into helping our end users to be as efficient and quick as possible to deal with their big orders (up to 400 line items per week).

Over the years the main industry we serve has focussed itself on wholesale gastronomy. If you have ever bought something in any of the bigger empolyee restaurants in any larger company, if you have ever bought something in any restaurant of any school or university in Switzerland, whatever you consumed has likely been procured and managed over one of our platforms.
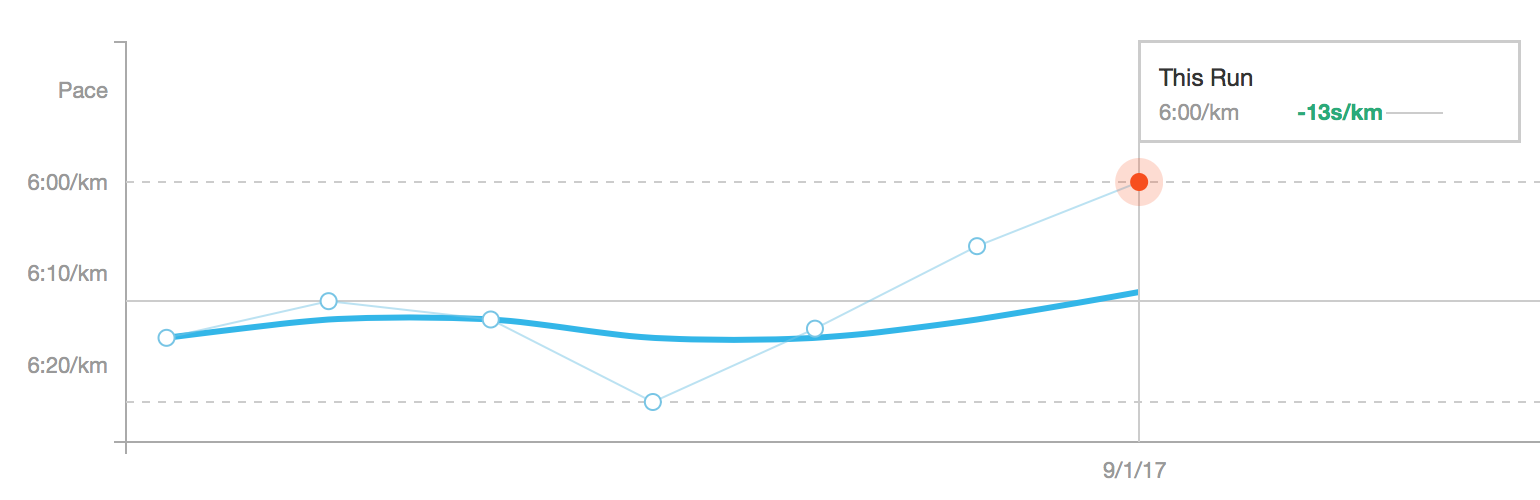
For our customers and ourselves, we handle a seizable amount of data (the largest data set is 3.2 TB in size).
I’m always calling our field «medium data» – while it might still fit into memory, it’s definitely too big to deal with it in the naïve way, so it’s not quite big-data yet, but it’s certainly in interesting spheres.
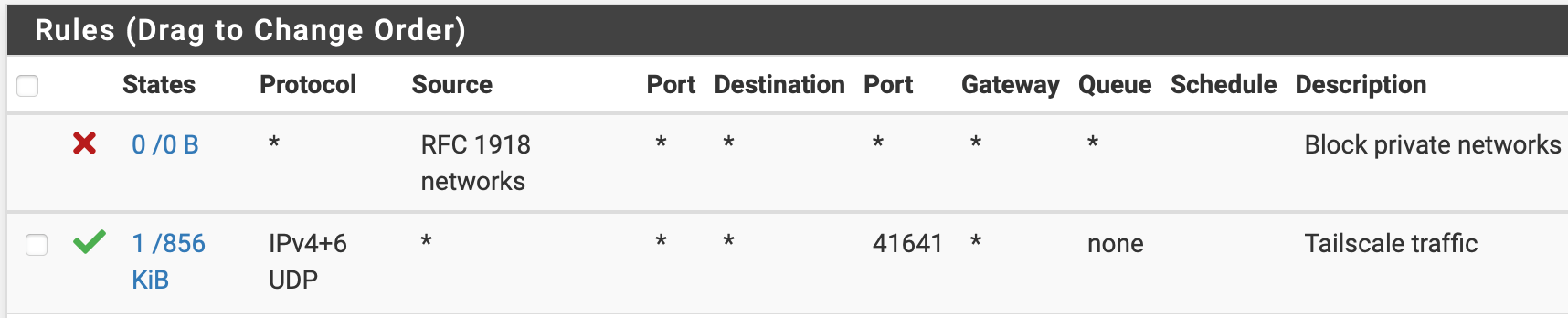
We’re in the comfortable position that the data entrusted to us is growing in the speed that we’re able to learn how to deal with it and so is our architecture. What started as a simple PHP-in-front-of-PostgreSQL deal back in 2004 by now has grown to a cluster of about 40 machines: Job queue servers, importer servers, application servers, media servers, event forwarding servers; because we are hosting our infrastructure for our customers, we can afford to go the extra mile to do things technically interesting and exciting.
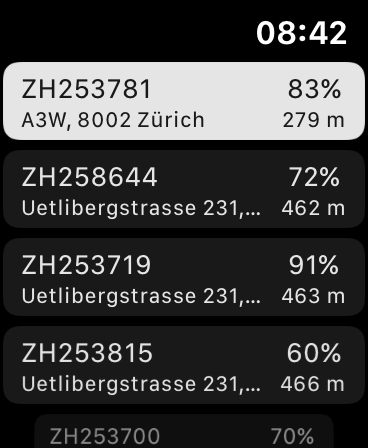
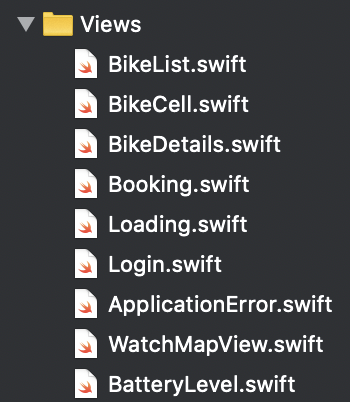
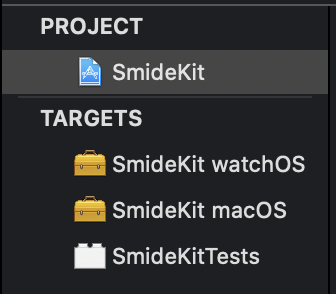
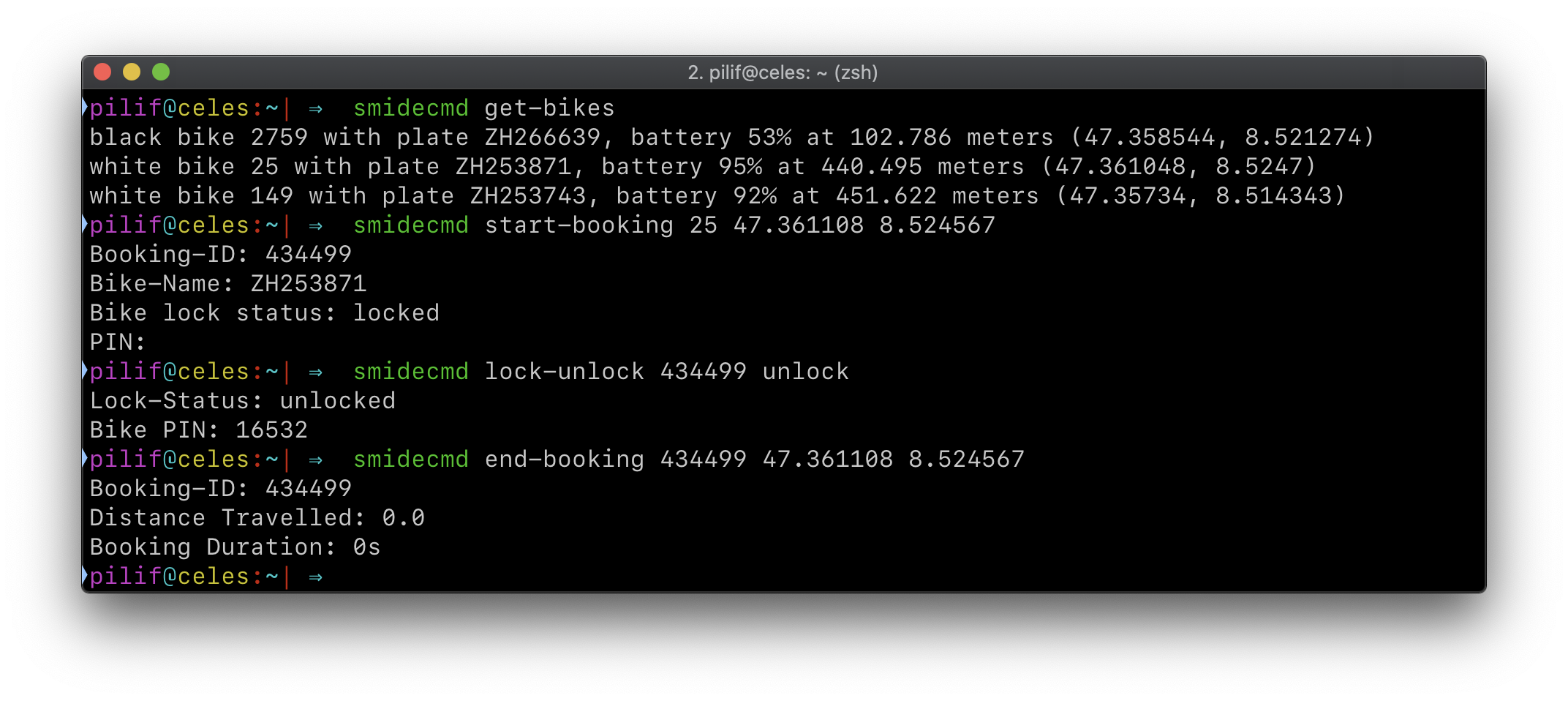
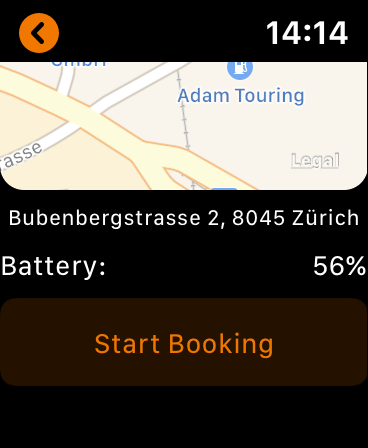
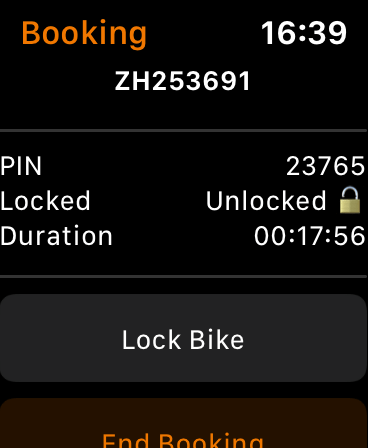
Speaking of infrastructure: We own the full stack of our product: Our web application, its connected micro services, our phone apps, our barcode reading apps, but also our backend infrastructure (which is kept up to date by Puppet)
While our main application is a beast of 250k lines of PHP code, we still strive to use the best tool for their jobs and in the last years have grown our infrastructure with tools we have written in Rust, JavaScript & TypeScript (via Node.js) and of course our mobile apps are written in their native languages Swift and Java with more and more Kotlin.
We try to stay as current as possible even with our core PHP code. We have upgraded PHP versions more or less the day they come out.
As strong believers in Open Source, whenever we come across a bug in our dependencies, we fix it and publish it upstream. Many of our team members have had their patches merged into PHP, Psalm, Rust, Tantivy and others. Giving back is only fair (and of course also helps us with future maintenance).

Over the years we have learned about the value of modern software development: Strong typing (even in PHP through Psalm), functional programming, automated tests, automated deployments: We do whatever we can do to allow us to continuously and with confidence push updates to our thousands of users multiple times a day.

If this sounds interesting to you and you want to help us make it possible for our end users to leave their workplace earlier because ordering is so much easier, then ping me at jobs@sensational.ch.
You should be familiar with working on bigger Software projects and understanding of software maintainability over the years. We hardly ever start fresh, but we constantly strive to keep what we have modern and up to speed with wherever technology goes.
You will be initially mostly working on our PHP and JS/TypeScript code-base, but if you’re into another language and it will help you solve a problem you’re having or your skill in a language we’re already working with can help us solve a problem, then you’re more than welcome to help.
If you have UNIX shell experience, that’s a bigger plus, though it’s not required, but you will just have to learn the ropes a bit.
All our work is tracked in git and we’re extremely into beautiful commit histories and thus heavy users of the full feature-set that git offers. But don’t worry – so far, we’ve helped everybody get up to speed.
And finally: As a mostly male team – after all, we only have two women working on our team of developers, we’d especially love if more women would find their way into our team.
All of us are very aware how difficult it is for minorities to find a comfortable working environment they can add their experiences to and where they can be themselves. All of us strive to provide such an environment.